dIMA 7005 conference fi1
e:1IIE:/
doub 1 e%20c 1 icJ<Olo20to%20start.lTable
of
Contents
ISBN: 0-9753393-4-6
Internet and Information Technology in
Modern Organizations:
Challenges & Answers
Proceedings of
The 5
thInternational Business Information Management
Association Conference
December 13 - 15, 2005
Cairo, Egypt
Editor
Khalid S. Soliman
International Business Information Management Association (IBIMA)
Copyright 20()5
...
Conference Chai r
Khalid S. Soliman
Hofstra
University,
USA
Program Chair
JBIMA 2,005 conference fi I
e:1IIE:I
double%20click%20to%20start.tSherif Kamel
American University in Cairo, Egypt
Imed Boughzala
GET Iinstitut National des Telecommunications, France
French Track Chair
Imed Boughzala
GET/lnstitut National des Telecommunications, France
Spanish Track Chair
Christiane E. Metzner
Universidad Central de Venezuela, Venezuela
Theory and Practice of Software Engi'neering (TPSE) Track.
Chair
Magdy Serour
University of Technology Sydney, Australia
TPSE Track Programme Co-Chairs
Brian Henderson-Sellers
University of Technology Sydney, Australia
Cesar Gonzalez-Perez
University of Technology Sydney, Australia
Conference Advisory Committee
John F. Affisco, Hofstra University, USA
Mel Damodaran, University of Houston-Victoria, USA
Reggie Davidrajuh, Stavanger University College, Norway
Zahir Irani, Brunei University, UK
Markus Mau, University of Giessen, Germany
Nicole Mau, University of Giessen, Germany
IBIMA 2.005 conference
lof8
file:IIIE:/double%20click%20to%20start.r
Mohammad Eyadat, California State University, USA
Krassie Petrova, Auckland University of Technology, New Zealand
Marcus Rothenberger, University of Nevada-Las Vegas, USA
Najib Saylani, Hofstra University, USA
Mark Srite, University of Wisconsin - Milwaukee, USA
Program Committee
Anastase Adonis, Objective Networks, France Vasilis Aggelis, Piraeus Bank, Greece
Mahmoud Arayssi, American University in Beirut, Lebanon Muhammad Fareed Arif, University of Central Punjab, Pakistan
Nabil Arman, Palestine Polytechnic University, Palestine
Muhammad Hasmi Abu Hassan Asaari, Universiti
Sains
Malaysia, Malaysia Sard Assar, I.N. T Evry, FranceRiem M. Hamdi Abdel Azim, German University in Cairo, Egypt Imad Baalbaki, American University in Beirut, Lebanon
Ali AI-Badi, Sultan Qaboos University, Oman
Abdul Hafeez-Baig, University of Southern Queensland, Australia Subflajit
Basu,
Queen's University Belfast, IrelandJean-Paul Van Belle, University of cape Town, SOlJth Africa Rob Bernard, Higher Colleges of Technology, UAE
John Byrne, RMIT Business, Australia
Silvia Elaluf-Calderwood, London School of Economics, UK Enrique V, Carrera, University San Francisco of Quito, Ecuador
Rommert J. Casimir, Tilburg University, The Netherlands Jan' Mendonca' Correa, Professor
at
University Of Brasilia, 'Brazil Lourdes Canos Daros, Universidad Politecnica de' Valencia, SpainSoumaya Ben Dhaol), Paris IX Dauphine University, France Patrick Doran, Zayed University, UAE
Jean-Louis Ermine, Institut National des Telecommunications, France Susana de Juana Espinosa, Universidad de Alicante, Spain Uchenna Eze, Nanyang Technological University, Singapore
Xiuzhen Feng, University of Twente, Netherland Eulalio G, Campelo Filho, University Karlsruhe, Germany Jose Luis Fuertes, Universidad Politecnica de Madrid, Spain
l'Jorjihan Abdul Ghani, University of Malaya, Malaysia Song Han, Curtin University of Technology, Australia Ramzi
A.
Haraty, Lebanese American University, LebanonSuraya Hamid, University of Malaya, Malaysia Markus Helfert, Dublin City University, Ireland Pilar Herrero, Universidad Politecnica de Madrid, Spain
Mohammed AI-Jadeed, University of Edinburgh, UK Lobna Jeribi, ENSI University, Tunisia Anand Jeyaraj, University of Missouri -St.Louis, USA Kevin Johnston, University of Cape Town, South Africa
Nazean Jomhari, University of Malaya, Malaysia Noorliza Karia, Universiti Sains Malaysia, Malaysia Mohammad Ayub Khan, Tec de Monterrey, Mexico
Rami Khasawneh, Lewis University, USA Matthew Nicolas Kreeger, University of
St,
Andrews, UKSupakorn Kungpisdan, Monash University, Australia Zaigham Mahmood, University of Derby, UK
IBIMA 4005 conference
t
of8
file:///E:/double%20cJick%20to%20start.l
Saeed AI-Maliki, University of East Ang/ia, UK Vicky Manthou, University of Macedonia, Greece Merdad
Mohasses,
Sharjah Women's Colleges, UAE Patrick Loh, Knowledgeworks Consultants, SingaporeKeri Logan, Massey University, New Zealand
Somaya
Ali, Qatar University, Qatar Thi Bac Nguyen, Monash University, AustraliaShastri L Nimmagadda, Wafra Joint Operations Company, Kuwait Thomas Nowey, University of Regensburg, Germany
Urban Nlllden, Goteborg University, Sweden Kok-Leong Ong, Deakin University, Australia
Roslina Othman, International Islamic University Malaysia, Malaysia Siew Hock Ow, University of Malaya, Malaysia
Roberto Paiano, Universita degli Studi di Leece, Italy Victor Pankratius, University of Karlsruhe, Germany
Alan R. Peslak, Penn State University
&
Nova Southeastern University, USA Ghassan AI-Qaimari, Universityof
Wol/ongong in Dubai, UAEHugo Rehesaar, University of New South Wales, Austra/ia Md. Mahbubur Rahim, Monash University, Australia
Sri Devi Ravana, University
of
Malaya, Malaysia Peter Rittgen, University Col/ege of Boras, SwedenTomislav Rozman, University
of
Maribor, Slovenia Mohammed Samaka, Qatar University, QatarHasan AI-Saedy, Skyline Col/ege, UAE
Samiaji
Sarosa,
Atma Jaya Yogyakarta University, Indonesia Jawahitha Sarabdeen, Multimedia University, Malaysia Francesca Sgobbi, Universita degli Studi di Brescia, ItalyMaha sィセォゥイL@ Zayed University, UAE .
. K.
Srikumar, Infdsys Technologies Ltd, 'India Ali AI-Solbi, University of East Anglia, UK Daniel Sommer, Universitat Karlsruhe, Germany Javier Soriano, Universidad Politecnica de Madrid, SpainMinwir AI-Shammari, Bahrain Univesity, Bahrain Lampros Stergioulas, Brunei University, UK
Amine Nehari Talet, King Fahd University of Petroleum
&
Minerals, KSA SabahN.
AbduLwahab AL- Tamimi, American Collegeof
Dubai, UAEPawan Kumar Taneja, Punjab College Of Technical Education, India 'Fadi Thabtah, University of Bradford, UK
Leonardo Jose Cortez Vil/amizar, Universidad Central de Venzuela; Venzuela William Yeoh, University of South Australia, Australia
Zijiang Yang, York University, Canada
S.
Venkateswarlu, KL College of Engineering, IndiaStuarl Warden, Cape Peninsula University
of
Technology, South Africa EdgarR.
Weippl, Vienna Universityof
Technology, AustriaDick Whiddett, Massey University, New Zealand Viaches/av Wolfengagen, Institute "JurlnfoR-MSU", Russia
Masoud Karami Zarandi, Tehran University,lran Roman Povalej, Universitat Karlsruhe, Germany
Silvana Quaglini, University of Pavia, Italy Jorge Valdes Conca, Universidad de Alicante, Spain
Shushma Patel, London South Bank University, UK Islam
A.
M. EI-Maddah, Ain Shams University, Egypt Soraya Kouadri Mostefaoui, Oxford Brookes University, UKJoo
Y.
Park, Yonsei University, Seoul, Korea Ozlem Bak, Universityof
Greenwich Business School, UKfBIMA 2005 conference
; of8
file:IIIE:/double%20click%20to%20start.t
Virginie Sans, I'universite de Cergy-Pontoise, France K. P. Lam, University of Keele, UK
Zokir Nazarov, Cardiff University, UK Ikram Amous, Universite de Sfax, Tunisia
Krassie Petro va, Auckland University of Technology, New Zealand Hasan
A.
Abbas, Kuwait University, KuwaitSue Foster, Monash University, Australia Fahim Akhter, Zayed University, UAE
Paulus Insap Santosa, Republic Polytechnic, Singapore Khamis Omar, Princess Sumaya University for Technology, Jordan Tahir Naeem, COMSA TS Institute of Information Technology, Pakistan
Kathy J. Liszka, University of Akron, USA Nixon Muganda, University of Cape Town, South Africa
Marite Kirikova, Rrgas Tehniska universitate, Latvia Samir Garbaya, Robotics Laboratory of Versailles, France
Dr Lawrence Green, University of Manchester, UK Khalid Khawaja, American University in Dubai, UAE Dr. Gregor Zellner, Universitat Regensburg, Germany
Katja Harej, University of Maribor, Slovenia Saad Harous, College of Arts & Sciences, UAE Mohamed Salah Hamdi, University of Qatar, Qatar
Mohamad Fauzan Noordin, International Islamic University Malaysia, Malaysia
Nihat Kasap, Sabanci University, Turkey Yahya H Alzoubi, Philadelphia University, Jordan Reggie Davidrajuh, University of Stavanger, Norway
Viii Podgorelec, University of Maribor, Slovenia Anthony Rhodes, Zayed University, UAE Shu Zhou, The University of New Mexico, USA
Fotis Liarokapis, City University, UK
Noor Raihan Ab Hamid, Multimedia University, Malaysia Jaiprakash T. Lallchandani,
D. D.
University, IndiaMarjan Druzovec, University of Maribor, Slovenia Gianmarco Radice, University of Glasgow, UK Euripidis N. Loukis, University of the Aegean, Greece Lepa Vrazalic, University of Wollongong in Dubai, UAE
Ahmad Kayed, Applied Science University, Jordan John Debenham, University of Technology-Sydney, Australia
Emad Bataineh, Zayed University, UAE
Yousef Shahwan, United Arab Emirates University, UAE Richard Chbeir, Universite de Bourgogne, France
Robert
rt
Barbour, Unitec, New ZealandHalim M. Khelala, University of Wollongong in Dubai, UAE Chew Esyin, University Malaya, Malaysia
Tran Khanh Dang, HoChiMinh City University of Technology, Vietnam Greg Skulmoski, Zayed University, UAE
Albert H
S
Scott, Vocational Training Council, Hong Kong Markos Kyritsis, BruneI University, UKAmin Yousef Noaman, King Abdulaziz University, KSA Salaheldin Ismail Salaheldin, Qatar University, Qatar
Sonali S. Morar, BruneI University, UK
Jae-Suk Yun, Korea Information Security Agency, Korea Ahmad Khasawneh, University of Newcastle, Australia
Hossein
S.
Zadeh, RMIT, AustraliaIBIMA セPPU@ conference
) of8
file:/IIE:/double%20click%20to%20start.'
Mulhim AI-Doori, American University in Dubai, UAE George Giannatos, Monash University, Australia Gordana Jovanovic Dolecek, Institute INA DE, Mexico Haitham Hmoud A/shibly, The University of Newcastle, Australia
Ahmed Guessoum, Univ. of Sharjah, UAE
Ammar Ahmed, CSIRO Manufacturing and Infrastructure Technology, Australia
Rinette Roets, University of Fort Hare, South Africa S,7amshul Bahri, University of Malaya, Malaysia Abdollah Aghaie, K N Taosi University of Technology, Iran
Fayez Ahmad Albadri, MGSM Macquarie Graduate School of Management, Australia
Teuta Cata, Northern Kentucky University, USA Ari M. Wah/stedt, University of Jyvaskyla, Finland Jorge Molea, Universidad Central de Venezuela, Venezuela
Hong Lin, University of Houston-Downtown, USA Roman Povalej, Universitat Karlsruhe, Germany
Dave Henderson, Virginia Polytechnic Institute
&
State University, USA Bala Srinivasan, Monash University, AustraliaKha/id Benbachir, Canada
Jaime Ramirez, Universidad Politecnica de Madrid, Spain Knolmayer Gerhard, Universitat Bern, Switzerland karim Bourouni, Ecole Nationaie d'ingenieurs de Tunis, Tunisia Ahmed EI-Raga/, Arab Academy for Science and Technology, Egypt Hanene Trichili, Ecole Nationale Superieure des Telecommunications de
Bretagne, France
Omar EI-Gayar, Dakota State University, USA Doha Abelkhaleq, ESKADENlA, Jordan
Tyng- Yeu Liang, National Kaohsiung University of Applied Sciences, Taiwan Sylwester Kozak, National Bank of Poland, Poland
Stefan Eicker, Universitt3t DUisburg-Essen, Germany Najib Saylani, Hofstra University, USA
Pankaj Kamthan, Concordia University, Canada Adel Ai-Alawi, University of Bahrain, Bahrian
Markus Bick, ESCP-EAP European School of Management, Germany Asad I. Khan, Monash University, Australia
Susan Koruth, CGI-Australia, Australia Mirja Pulkkinen, University of Jyvt3skyla, Finland Ra'ed Moh'd Masa'deh, Nottingham University, UK
Al1med Subaih, University of Sheffield, UK Berta Batista, Insh"tuto Politecnico do Porto, Portugal Hajo Reijers, Eindhoven Unversity of Technology, Netherlands
Christine Verdier, Universite Lumiere Lyon
2,
France Akram AI-Rawi, Zayed University, UAE Massimo De Santo, Universita di Salerno, Italy Joao Rocha, Instituto Po/itecnico do Porto, PortugalHonglei Li Violah, The Chinese University of Hong Kong, Hong Kong Alexei Tretiakov, Massey University, New Zealand
Nicolas Larrieu, KAIST University, Korea Tania Pavlou, City University London, UK Iryna Skrypnyk, University of Jyvaskyla, Finland
Azzedine Lansari, Zayed University, UAE Jacek Plodzien, Polish Academy of SCiences, Poland
Ari P. Hirvonen, TietoEnator, Finland
IBIMA :?005 conference
70f8
tile:IIIE:/double%20click%20to%20start.l
Djamel Khadraoui, CRP Henri Tudor, Luxembourg Chiou-Pirng (Ping) Wang, Albany State University, USA Laurel Evelyn Dyson, University of Technology-Sydney, Australia
Rui (Ray) Chen,
State
University of New York at Buffalo, USA Abdelaziz Khadraoui, University of Geneva, Switzerland M.F. Lau, Swinburne University of Technology, AustraliaDavid
A
Bray, Emory University, USA Snene Mehdi, University of Geneva, Switzerland Roland Kaschek, Massey University, New ZealandKhalil
A
Abuosba, The Arab Academy for Banking and Financial Sciences, JordanVanessa
Chang, Curtin University of Technology, Australia Damir Kalpic, University of Zagreb, CroatiaDhayalan Velauthapiflai, University College of Bergen, Norway Mahbubur Rahman Syed, Minnesota
State
University, USAKevin
K.
W HO, The Hong Kong University of Science and Technology, Hong KongDeb S/edgianowski, Hofstra University, USA Az-Eddine Bennani, Reims Management School, France
Settapong Mafisuwan, Chulachomklao Royal Military Academy, Thailand Gerald
C.
Gonsalves, College of Charleston, USAHenry B. Wolfe, University of Otago, New Zealand
Sam
Lubbe, University of KwaZulu-Natal, Durban, South Africa Nabil Mzoughi, ISG of Sousse, TunisiaJose Diego De la Cruz, LEcole Poly technique Federale de Lausanne, Switzerland
Upasana G Singh, University of KwaZulu-Natal, South Africa Judith Pavon Mendoza, Universidade de
Sao
Paulo, Brazil WojciechR,
The Poznan University of EconomiGs, Poland Naveed Ahmed Khan, COMSATS Institute of Information Technology,. Pakistan
Yahya Slim ani, University of Tunis EI Manar, Tunisia
Vass
Karpathiou, RMIT University, Australia Isabel!e Comyn-Wattiau, ESSEC, FranceXin Lucie
Li,
The University of North Carolinaat
Pembroke, USAAnastase
Adonis, Objective Networks, France Damminda Alahakoon, Monash University, AustraliaRegina Connolly, Dublin City University, Ireland
Scott
Rathbone, CGI, AustraliaShushma Patel, London South Bank University, UK Alcina Prata, Inst/tuto Politecn/co de SetUbal, Portugal Emmanuel Matthew, University of Wollongong, Australia Ann Johansson, University of TrollhSttanlUddeva/la, Sweden
Loay Sehwail, Oklahoma State University, USA
Inas
E.
Ezz, Sadat Academy for MgtSc.,
Egypt and BruneI University, UK Indrawati Nataatmadja, University of Technology-Sydney, AustraliaSagarmay Deb, University of Ballarat, Australia Ela Klecun, London School of Economics, UK Wenshin Chen, Prairie View A&M University, USA
TPSE Track Programme Committee
IBIMA :?005 conference
セ@ of8
file:IIIE:/double%20click%20to%20start.l
Andreas Opdahl, University
of
Bergen Bashar Nuseibeh, The Open University Bhuvan Unhelkar, Universityof
Western SydneyBran Selic, IBM Rational
Brian Henderson-Sellers, University
of
Technology, Sydney Cesar Gonzalez-Perez, Universityof
Technology, SydneyColette Rolland, Universile Paris
1 -
Pantheon Sorbonne Colin Atkinson, Universityof
MannheimDarryl Winder, The Institute for Exil Planning David Lowe, University
of
Technology, Sydney Didar Zowghi, Universityof
Technology, SydneyDilip Patel, London South Bank University Donald Firesmith, Software Engineering Institute Francisco Ruiz Gonzalez, Universidad de Castilla-La Mancha
Franck Barbier, Universile de Pau et des Pays de I'Adour George Feuerlicht, Unwersity
of
Technology, SydneyGraham Low, University
of
New Soulh Wales Houman YounessiIan Graham, TriReme International
Igor Hawryszkiewycz, University of Technology, Sydney Jack Greenfield, Microsoft
Jean-Michel Bruel, Universite de Pau et des Pays de I'Adour Jeff Sutherland
John D. McGregor, Clemson University Jolita Ralyte, University
of
GenevaJudy Bamberger Karl Wiegers," Process Impact
Khalil Abuosba, The Arab ACEldemy for Banking and Financial Sciences Magpy Serour, University
of
Technology, Sydney6scar Paslor Lopez, Universidad Politecnica de Valencia Pavel Hruby, Microsoft
Phil Haynes, Virtvalnation Pty Ltd Scott Ambler, independent consultant Sjaak Brinkkemper, Vrije Universiteit Amsterdam
Stephen Mellor Tony Wasserman
Victor Pankratius, University
of
KarlsruheCopyright
@
2005 International Business Information Management Association Individual authors retain copyright on papers. Please contact the authors directly forreprint permission
Table of Content
file:!1IE:/table.l
Table of Contents
Supply Chain Management
The Role of Emergent Information Systems in EnablingSupply Chain Agility: Dealing With Change, Uncertainty, and Complexity
Zaher Mohdzain and Andrew White
Modelling Smart Label-Supported Production Processes
Bernd Scholz-Reiter, Torsten Hildebrandt, Jan Kolditz, and Hartmut Hohns Supporting Information Mobility in the Fresh Produce e-Supply Chain
loannis Manikas, Dimitris Folinas, Tania Pavlou, and Basil Manos
Determinants and Performance of Electronic Partnership between Buyer and Suppiier Young-Jin Choi
The evolution of knowledge capabilities in third party e-fulfilment companies Paul Alexander
Supply Chain Strategic Management USing Transformed Balanced ScoreCard Mohammad Jafar Tarokh and Davood Farajian Shooshtari
E-Government
IntrodUCing Communication Space Lars-Olof Johansson and Aron Ha!lborg
The potential positive impact of E-government projects - The Flemish Environmental Legislation Navigator: Conclusions of an inquiry about the use and the benefit of an on-line legal environmental expert system
Geert De Meyer, L. Lavrysen, and G. Van Eetvelde
e-Services in Government: Why we need Strategies for Capacity Building and Capacity utilization? Girija Krishnaswamy
The Commitment Generation Process In The G2C Online Relationships Luis V. Casal6, Carlos Flavitm, and Miguel Guinaifu
The economic impact of e-government initiative (G2B) as a tool of ICT upon SMEs in Jordan Ra'ed (Moh'd Taisir) Masa'deh and Emad M. AI-kharabsheh
Joined-up Government: Current Trends and Applications in e-Government and eHea.lth D. D. Pappa and
L.K.
StergioulasBusiness Process Reengineering
Table of Content fi le:IIIE:/table.l
Is Business Process Management an Incarnation of Business Process Reengineering? Leila Jamel Menzli. Sonia Ayachi Ghannouchi. and Henda Hadjami Ben Ghezala
Intelligent Product Change Management - Production Network Perspectives for the Ramp-up Phase Bernd Scholz-Reiter. Hartmut Hbhns. Farian Krohne, and Bing Leng
Paper Usage Management and Information Technology: An Environmental Case Study at an Australian University Venn Hardy. Ho Chung Fung. Guang Sheng Xian, Jing Hua Wu, Xiao Van Zhang. Laurel Evelyn Dyson
Simulation Study of a Distributed Control Scheme in Flexible ManlJfacturing Systems Dania
A.
EI-KebbeKnowledge Management
Factors Affecting Successful Implementation of Intranet Based Knowledge Management Systems Norlida Buniyamin and Za!nuddin Mohamad
Need-finding through Narrative Inquiry in Systems Design Holst Marita and Anna Stahlbrbst
Learning across Bcundaries: Developments towards a European Framework for ICT Skills Peter Wei!!. Roman Povalej, and Wolffried Stucky
Getting Knowledge Measured, Getting Knowledge m。ョセ@ Ivy Chan, Matsuba NG, and C.
K.
FOK JacksonIT and Psychosocial Occupational Risks: a Delphi Study
Mario Arias Oliva, Teresa Torres Coronas, Mar Souto Romero, and Rosa Queralt
DevelQQment of Knowledge Management System: A Preliminary Study" on Property Management Companies in Malaysia
Muhammad Najib Razali and Zaharah Manaf
Conceptualised Models of Detailed Knowiedge Structures For Different Business Operations Craig A Godley
Jhe Effect of Information Sharimon Empo't{enIlent in Indonesia
v
AjiHermawan
Enterprise Integeration
A Maturity Model Framework for Assessing Organizational Processesin Enterprise Integration of Innovative Iechnology
Garth
R.
MacKenzieA Case Study: Enhancing Enterprise System Competitive Advantage Ameena Zafar
Table of Content
file:IIIE:/table.IManaging Enterprise Systems Integration in Corporate Mergers and Acquisitions - A Tentative Framework and the Case of TIH
Stefan Henningsson
IT Outsourcing
IT Outsourcing - An Analysis of the State-of-the-Art Michael Amberg, Nadja HoBbach, and Martin Wiener
SME
SMEs in developing Economies - Challenges and Strategies for Enterprise Systems Integration Suhas Raut, Deepak B, Phatak, and
A
R.
YardiElectronic Commerce Adoption and Strategic Alliance Membership: A Study of Regional SMEs in Sweden Robert MacGregor and Lejla Vrazalic
The Impact of IT investment in RSA e-Cornmerce SME Organizations Sam Lubbe
Database
and·
Data Management
A Database Querying Tool for NaIve Users
Solange Nice Alves de Souza, Edit Grassiani Lino de Campos, Luiz Sergio de Souza, Andre Roberto Doreto dos Santos
A Heuristic Object-Oriented Data Schema for Contextual Accounting Mohamed EI-Badawi, Myron Sheu, and Wang C, Wong
The Application of Grid and Agent Technology in CBR Nie Guihua and Liu Pingfeng
Modeling of Updating Moving Object Database Using Timed Petri net Model FATorky, N, Abd el-Wahed, HM, Abdulkader, and WEI-Kholy
E-banking & Finanical Industry
Application and Diachronic Strength of e-Trans Association Rules Vasilis Aggelis
Banking Technology Balanced Scorecard: A Model for Evaluating Banking Technology Effectiveness Lawrence Harold and Thenmozhi
Table of Content file:IIIE:ltable.l
Beyond the Resource-Based View of the Firm: The Case of Dynamic Capabilities Building at a Saudi Bank Mohammed AI-Jadeed and Alfonso Molina
Multi-Dimensional Role of Trust in I nternet Banking Adoption Shumaila Yousafzai
Strategic Networks to Create e-Banking Value: The Case of a Saudi-European Joint Venture Bank Mohammed AI-Jadeed and Alfonso Molina
M-Commerce
Adoption Factors for Mobile Gaming in South Africa Stanley Van Wyk and Jean-Paul Van Belle
The Impact of Uplink CapacityJQJ:;ell Coverage in WCDMA Mobile Internet Napaporn Petchinda, Settapong Malisuwan, and Arisa Rojnuckarin
Adoption of RFID in Logistics - A Case Study in the Field of Automobile Logistics Felix Bose and Wolf Lampe
Capacity of the WCDMA-FDD Mobile Internet in Hiah-Mobility Environment
Napaporn Petchinda, Settapong Maiisuwan, Panitee Ritthiruangdech, and Vic hate Ungvichian
Intelligent Secure Management of Electric Power Organizations: Data Collection Using Mobile Agents Radwan Tahboub, Vasile Lazarescu, and Imane A. Ns。セッゥエ@
Exploring factors affecting the adoption of mobile Internet in Jordan: Empirical Study Ahmad Khasawneh, Patricia Gillard, and Brian Regan
§aving Cost of Ownership for RTA C41 Systems by Utilizing Commercial Satellite Systems Anupon Boriboon, Settapong Malisuwan, Chanawat Phadwichit, and Porakrit Saihassadee
A Framework for QoS-aware m-Commerce Abdelnasser M. Abdelaal and Hesham H. Ali
Location-Determination System for Enabling M-Commerce Applications Moustafa Youssef and Ashok Agrawala
A Preliminary Research Model of Thai Mobile Market Structure
Settapong Malisuwan, Kulthon Kasemsan, Ussanee Malisuwan, and Dulyalak Phuangthong Leveraging Radio Frequency Identification (RFIO) Technology for Halal Tracking Tag
Azah Anir bt Norman
Com puter Networks and Remote Access
Modifications to Bandwidth Allocation Algorithms to Satisfy Remote Access Services Requirements Mohammed Attya Khaliefa, Ali Ali Fahmy, Iman A/y Saroit Ismail, and Tarek Abd EI-Megeed
Table of Content file://IE:ltableJ
Local-Communities Insertion Network Platform: Design and Specifications Djamel Khadraoui, Evren Bulut, Raul Ruggia, Federico Piedrabuena, and Farid Meinkohn
Congestion Control for a Better Performance of Computer Networks Atef Zaki Ghalwash and Sally Osama Anwar
E-Business
A Holistic Framework beyond Traditional Approaches of E-Business Research Practice Az-Eddine Bennani
The Current State of E-Commerce in Jordan - Applicabiliiy and Future Prospects: An Empirical Study Rifat O. Shannak and Mu'taz M. AI-Debei
Impediments of E-business - a Dubai Experience Aisha Ali AI-Alawi, Joze Kuzic, and Mehmood Ahmad Chadhar
Planning and Managing the Organizational Key Success Factors for the Transformation to E-business Environment Magdy Kodsy Serour
Scope and Potential of Teleshoping in India: Case Study of Punjab State Gautam Bansal and Sandhir Sharma
Challenges to an E-Business Model: Pre- and PQst-Adoption Mohamad Fauzan Noordin and Roslina Othman
What Are The Strategic Choices of Electronic Marketplace Functionalities? Sebastien Tran
E-readiness in developing countries: A conceptual e-readiness framework for small tourisr:l enterprises Stan Karanasios and Stephen Burgess
Software Development
Increasing Human-Centred Software Development Maturity in Software Development Organizations Ghassan AL-Qaimari
Metaphors in Co-Design Peter Rittgen
Increasing Efficiency in Service Oriented Architecture Amir Malik
A Test Cases Generation Technique Using Genetic Algorithms Arabi Keshk, Ahmed M. Omira, Nabil
A.
Ismail, and FawzyA.
TorkeyOn-Line Handwritten Character Recognition: An Overview Arnan Deep
Understanding Requirements Engineering Process: a Challenge for Practice and Education Lemai Nguyen, Jocelyn Armarego, and Paul Swatman
Table of Content file:!IIE:/tableJ
Prosody Generation In Concatenation Malay Language Speech Synthesizer (CMSS)
Siew Hock Ow, Roziati Zainuddin, and Wai Keong Loo
Extreme Cots-Based Software Development Process: A Process Enhancement
Maree Mujeeb-u-Rehman, Abdul Wasim Shaikh, and Memon Abdul Ghafoor
Broker-Oriented Software Development Process from Cots Products -A Process Enhancement
Abdul Wasim Shaikh and Maree Mujeeb-u-Rehman
Challenging the Rules: An Investig9tion of a Fact-BasecL6J:mrQach for Specifying Business Rules
Adrian Hargreaves
An approach to the Human Values Scale from Smart User Models
Javier Guzman-Obando, Gustavo Gonzalez, Josep Lluis de la Rosa, Silvana V. Aciar, Ronald U.
RUlZ,
Jose A.
Castan
Artificial Intelligence
Conversion of a Fuzzy System to Balanced Scorecard System to improve Management Business
Ronald Uriel Ruiz Ordonez, Josep Lluis De La Rosa I Esteva, Javier Guzman Obando, and Victor Manuel Ardila
Soto
Comparing the Performance of Artificial Immune System and Self-Organizing Map Approaches to Anomaly
Detection
Atef Z. Ghalwash, Aliaa A. A. Youssif, and Samir A. Mohamed
An Intelligent Agent-Based Digital Currency Scheme
Mohamed Aborizka, Mohamed Kouta, Krishna Kavi, and Sherif Saad
Certain Bayesian Network based on Fuzzy knowledge Bases
Abdelkader Heni, Mohamed-Nazih Omri, and Adel M. Alimi
Information Systems in Healthcare Industry
Contribution and Limits of
UML
Models for Task Modelling in a Complex Organizational Context: Case Study in the
Healthcare Domain
Stephanie Bernonville, Christophe Kolski, and Marie-Catherine Beuscart
A web-based Automated Dental Identification System (webADIS)
Satyasrinivas Chekuri, Diaa Eldin M. Nassar, Ayman A. Abaza, Ali Bahu, and Hany
H.Ammar
E-Health: The New Frontier in Healthcare Management
Hesham O. Dinana and Hatem M. EI Ghamry
Corporate Perform ance Management
Corporate Performance Management: Alignment of Information Technology and Organizational Strategies
Khalid S. Soliman and Tanya C. Myers
Table of Content file:! / !E:/table.l
Information Systems Service
&
Quality Management
A Conceptual Framework for Quality Management in Information Systems Khalid I. AI-Shitri and Pam Mayhew
Emerging Issues in IT Service Management Sharman Lichtenstein, Lemai Nguyen, and Alexia Hunter
ERP
Statistical solution for risk management in the implementation of IMIS Adam Wasilewski
The ERP Systems Benefits for the Strategic Decisions Support in the Case of Tunisian Service Nedra Bahri and NabiJ Mzoughi
ERP systems and ROI analysis Adam Wasilewski and Eliza Wrobel
CRM
CRM systems: A Learning Perspective on How Organisations Manage to Understand the Customer Thomas Kalling and Lisen Selander
Electronic Customer Relationship Management (e-CRM): A Strategic Approach to Managing Customer Relationship Forough Karimi and Reza Sarkhosh
Selection Information Sources Based on the Trust of Similar Sources
Silvana Aciar, Josefina L6pez Herrera, Josep LLuis de la Rosa, Javier Guzman Obando, and Ronald Ruiz Ordonez
The Impact of CRM on Customer Loyalty, Retention and Firm Profitability: Modelling with Structural Equations in the Case of the Pharmaceutical Industry
Nabil Mzoughi and Nedra Bahri
Outsou rcing
Management of Critical Success Factors for Offshore Software Development Projects - A German Perspective Michael Amberg and Martin Wiener
Lifecycle of Outsourcing Relationship - A Multiple Case Study Approach Teuta Cata and Vijay Raghavan
Table of Content fiJe:I/IE:/tabJeJ
Data Mining
An Algorithm for Extracting the Root of Arabic Words
Sameh Ghwanmeh, Riyad AI-Shalabi, Ghassan Kanaan, Khalid Khanfar, and Saif Rabab'ah Question Answering Arabic System based on Passage Selection
Riyad AI-Shalabi, Ghassan Kanaan, Linda Jahjah
Using Cluster Analysis in Classification of Categories: Evidence from the Holly Qur'an Shahinaz Kamal and Ahmed EI Ragal
A New Technique for Automatic Text Categorization for Arabic Documents Samir
A.
Mohamed, Walaa Ata, and Nevin DarwishAutomatic Text Classification using NaIve Bayesian Aigorithm on Arabic Language Ghassan Ghazi Kanaan, Riyad Farhan Alsha!abi, and Omar Ghazi AI - Azzam
An information Retrieval System Based On Various Indexing Schemes
Ahmed
A.
A. Radwan, BahgatA.
Abdel Latef, Abdel Mgeid p... AU, and OsmanA.
Sadek A Feature extraction method for automatic web page classification system Eman M. Gmaleldeen, NabilA.
Ismail, Mohiey Hadhoud, and KamelA.
Mostafa]3yle Pruning in Associative Classification Mining Fadi Thabtah
Internet
J
WWW
Causes of I nternet Addiction: Boredom or Loneliness Shafqat Hameed and Carolyn Adagala
The Website Features and Categories in the Context of Fortune e-50 Companies Teuta Cata
Web Globalization: A Methodology for Develo..Qjng Usable Websites for the Global Market Ghassan AI-Qaimari
Web Usability: An Evaluation of the Governments' Websites in Sabah, Malaysia Muzaffar Hamzah
Web Site Reliability in Web Commerce Applications Hasan AI-Saedy
An Innovative Model for Providing Digital Connectivity to Rural Areas Abdelnasser M. Abdelaal and Hesham
H.
AliCultural Issues on Global Websites and Aspect-Oriented Requirements Engineering Kyeong Kang and Joao Araujo
Digital Versus Traditional Press: An Analysis of Readers' Motivations Carlos Flavian Blanco and Raquel Gurrea Sarasa
Table of Content file:/ / /E:/table.l
!does Browsers' Quality affect Websites' Functionality
Rania Maher Kilany Abd Elazez and Hawaf Abd AIHakim Teleb
The nearest some of us will ever come to Information Heaven
BK Ngubane, S Lubbe, and R Klopper
Toward an Assessment of Web Engineering Risks
Bouchaib Bahli and Dany Di Tullio
Information Systems Security
Development of Methodology for Evaluation of Information Security Level in CliP (Critical Information Infrastructure
Protection)
Bok-Ki Min, Jong-Whoi Shin, Kwang-Hee Choi, Kang-Shin Lee, and Jae-II Lee
The Bluetooth Needs Braces "A White Hat IT Security Risk Management Approach"
Khaled E. A. Negm
Making Sense of Web Services Security Issues
Stephen Humphreys and Maurice Abi-Raad
Effective Real Time Hybrid Threat Management Using Vulnerability Correlation
Khaled E. A. Negm
A Conceptual Framework for Preventing Tsunami-Like Damage of information Malice: A Human-Factor Approach
Chiou-Pirng Wang, Don Snyder, Kathaleena Monds
Addressing Enterprise Information Security
Anthony Rhodes
Learning Organization
Model LOB-MUT: Build up a Learning Organisation
Roman Povalej and Wolffried Stucky
Data Warehousing
Warehousing of Object Oriented Petroleum Data for Knowledge Mapping
Shastri L Nimmagadda, Heinz Dreher, and Amit Rudra
Towards A Generic Conceptual Model for Data Warehouses
Neveen EI Gamal, Ali EI Bastawissy, and Galal Galal-Edeen
E-Learning
Table of Content fi le:IIIE:/table.l
Integration of Knowledge Management and E-Learning: A Case Study on Tourism Authority of Thailand Ussanee Malisuwan, Kulthon Kasemsan, and Settapong Malisuwan
Trust and Privacy Issues
Towards Dynamic Control of Users Privacy Amr Ali Eldin, Rene Wagenaar, and Harry Bouwman
Perceptions on SPAM in a South African context
Wallace Chigona, Ashvin Bheekun, Meianie Spath, Saba Derakhashani, and Jean-Paul Van Belle Trust in mobile context aware systems
Semir Daskapan, Amr Ali eセ、ゥョL@ and Rene W. Wagenaar
Information Systems Research
IS Integration in Corporate M&A: Applicability of Related Theory and Future Advancements of the Research Field Stefan Henningsson
Stages of Growth Theory Revisited: Senior Management on Information Systems and Technology Alan Sixsmith and Gordana Culjak .
Perception and/or Individual Difference: What Affects the Acceptance of New Technology? Khaled Dahawy and Sherif Kamel
Changing User Requirements in an Inter··Organisationallnformation System Raija Halonen
IS Strategic Planning
Developing an ICT Strategic Plan for an African Utility 9orporation Kevin Allan Johnston
Special Tracks
Theory and Practice of Software Engineering (TPSE) Track
Project management improvement in Extreme Programming Houda Zouari Ounaies, Yassine Jamoussi, and Mohamed Ben Ahmed
Modularized Report Form Development Methodology in UFIDA Service-Oriented System-NC 3.0 Chen XueSong and Xu Hua
Table of Content
fi
le:///E:/table.lDatabase-Assisted Project Management Applied to Software Development Projects of Maritime Research and
Consultation Center (MRCC)
Hend Abdel Halim Hafez
ExPloring Varying Group Size on Software Inspection Performance: Preliminary Evidence from a Laboratory
.Experiment
Peter Patara , Nicholas Jit Chang Yaw, and Lesley Pek Wee Land
An approach for creating project-specific soft,!-,are developmenlmethogologies
Marko Bajec, Damjan Vavpotic, and Marjan Krisper
8
Simple Metric to Measure Semantic Overlap between Models: Application and Visualization
Jean-Paul Van Belle
An Infrastructure for UML Model Animation
Jose Saez, Ambrosio Toval, and Francisco Maestre
Towards Developing a Software Inspection Model: Preliminary Empirical Evidence
Matthew Reggers, Lesley Pek Wee Land, and Bernard Wong
Conceptual Model for Socio-technical Evaluation of Software Development Methodologies
Damjan Vavpotic, Marko Bajec, and Marjan Krisper
Components Behaviour Specification and Validation with Abstract States Machines
Goiuria'Sagardui, Xabier Aretxandieta, and Leire Etxeberria
A Pre-mortem on Post-mortems
John McAvoy
Evolution of Software Engineering Education'in Canada
Siamak Rezaei
A Framework for Representation of Software Patterns
Pankaj Kamthan
A global approach for consoiidating Trust-centric requirements in Large Collaborative Spaces
A. Adonis, K Drira, J.M. Rosario, and
.J.R.
Silva
Bringing Smailtalk Blocks to Java through Transformation Techniques
Mina Askari and Raihan AI-Ekram
Information Systems Research in French Track
Le droit d'auteur dans la societe d'information
Lotti Harnzi
M3C: Une Methodologie de Cartographie des Connaissances Critiques dans I'entreprise
Thierno Tounkara, Imed Boughzala, et Jean-Louis Ermine
Application de I'approche des Stakeholders au management du e-gouvernement
Table of Content file:IIIE:/table.l
Soumaya Intissar Ben Dhaou et Yousra Essid
Bases de donnees: fiabilite et perennite Tarik Beldjilali
I ndexation des images rm§dicales par Ie tatouage
Hanene Trichili, Mohamed Salim Bouhlil, Imen Fourati, et Bassel Solaiman
Vel's un Modele Integre de Gestion des Communautes Virtuelies Professionnelles Thierry Isckia, Thierno Tcunkara, and Imed Boughzala
Vers une Approche d'Architecture d'un Systeme Hypermedia Adaptatif
Zayani Corinne Arne!, Sedes Florence, Canut Marie-Fran<;oise, Amous Ikram, et Peninou Andre
Besoin de reconceptualisation de la culture organisationnelle dans les recherches en Systeme d'information Yousra Essid and Soumaya Intissar Ben Dhaou
Le tatouage des informations pour la protection de la propriete inteliectuelle Hanene Trichili, Mohamed Salim Bouhlel, et Bassel Soliaiman
E-Gouvernement dans un pays emergent: la Tunisie :Pour une integration de la perception des citoyens Asrna Chaouch
Information Systems Research in Spanish Track
Calidad De Datos - De La Teoria A La Practica
Edit Grassiani Lino de Campos, Solange N, Alves de Souza, Luiz Se'rgio de Souza, Judith Pav6n, Vera Lucia R Y.
,
sセセ@,
Tutorials
Software Architecture Metrics Hany
H.
AmmarMethod Engineering
Magdy Serour, Brian Henderson-Sellers, and Cesar Gonzalez-Perez
End of Table
Internet and Information Technology in Modern Organizations: Challenges & Answers 348
The Effect of Information Sharing on Empowerment in Indonesia
Aji Hermawan
Lecturer, Department of Agroindustrial Technology, Bogor Agricultural University, Indonesia and Doctoral Researcher, Manchester Business School, United Kingdom. Email: [email protected]
Abstract
This study examines the differences in information sharing and psychological empowerment in organisations, as well as the relationship of both. Using multiple case study research in four manufacturing companies in Indonesia, this study found that the levels and the relationships are different across the companies studied. The differences are explained by the extensiveness use of empowering initiatives and the contextual factors surrounding the companies. The limitations
of the universal measures of information and empowerment are also discussed ..
1. Introduction
This paper is a part of a wider study about empowerment theory and practices in Indonesia. Empowerment has been extensively studied and it might be the most popular term used across disciplines in the 1990s. This paper focuses on the reiationship between information sharing which is regarded as a part of structural empowerment -and psychological empowerment.
The relationship between information sharing and empowerment is well supported in management literature. To·empower organisations it is believed that more information should be available to more people at more levels ·through more devices. Such information might iHclude data about workflow, productivity, external environment, competition, and firm strategy. According to Bowen and Lawler (1992), there are two specific pieces of information, which are critical to empowerment:
(I) information about organisation's mission and (2) information about performance of a work unit Spreitzer (1995, 1996) shows that access to information is significantly related to empowerment. Individuals who perceive that they have a high degree of access to information report a higher level of empowerment than those who perceive they have less access to information. Additionally, the effects of empowerment on organisational performance are widely recognised. Empowerment is believed as mediator for performance by many writers such as Spreitzer (1995), Spreitzer et al (1997), Spreitzer et al (1999), Fuller et al ( 1999), Koberg et al ( 1999), and Kraimer et al (1999).
This paper aims to examine (I) the variations of information sharing and psychological empowerment, and (2) the effect of information sharing on psychological empowerment in four manufacturing companies in Indonesia.
2. Methods
This study used mUltiple case study research. There were four cases selected from the
manufacturing sector in Indonesia. As a case study research, the cases were not selected on the basis of statistical sampling, but it used the principle of maximum variation by including compar.ies from different industrial sectors and differenl technologies. The four companies were FoodCo, StelCo, Chem-Co, and WoodCo (the names are disguised). A combination of data collection methods was used in this study. This combination or triangulation was expected to be highly synergistic (Yin, 1994). The multiple data collection methods were used including: (1) interviews and (2) questionnaires. Mainly semistructured interview was used because it would make the interview move freely and more conversational but the focus on predetermined questions were able to be maintained. The questions were openended to allow respondents to say freely whatever they wanted to say. To achieve this, some interview ァオゥ、・セ@ were developed. All interviews were recorded and transcribed. The interviews were conducted with (a) senior managers and (d) employees. Senior manager expected to involve was senior human イ・セッオイ」・@ manager since he/she was the person responsible for the issues. The employees were asked about their perception of empowerment and information sharing. The interviews were conducted in order to yield more information than could be obtained from the questionnaire.
Questionnaires were used to obtain quantitative data on information sharing and psychological empowerment. The number of participating respondents depended on the number of employees occupying supervisory levels (below managerial levels) in the companies. There was no sampling taken since the questionnaire distributed to all employees at the levels. The questionnaire consists of questions about psychological empowermen1 and information sharing. The detail of each questionnaire is described below.
Internet and Information Technology in Modern Organizations: Challenges & Answers 349
averaging the number of the types of information the employees receive.
Psychological empowerment. To measure this aspect, Spreitzer's questionnaire, which has been widely used in measuring psychological empowerment, was employed. Because it has been widely accepted, Spreitzer'S construct has proved its validity and reliability in much research in the field of organisational behaviour. Even though there are many criticisms of this concept, there is a lack of alternative concepts that have been validated empirically. The mere comprehensive measure is difficult to develop and it is realised by its critics such as Zimmerman (1995, 2000). The weaknesses of this construct for not including interpersonal and behavioural components can be handled by including the structural dimension of empowerment, which will be described later. Spreitzer's questionnaire measures psychological empowerment including senses of meaning, competence, selfdetermination, and impact. The definitions of each component, as discussed in previous chapter. are as follows:
• Meaning is defined as the value of a work goal or purpose, judged in relation to an individual's own ideals and standards.
• Competence or selfefficacv is the selfbelief that one possesses the skills and abilities necessary to perform a job or task well. • Selfdetermination is an individual sense of
having choice in initiating and regulating actions or a feeling of having control over one's own work.
• Impact is the belief that one has significant influence ·over strategic, administrative, or operational outcomes at work (Spreitzer,
1995).
Based on the definitions, Spreitzer's questionnaire composes 12 (twelve) questions in 7point Likert scale.
The characteristic of the company, the number of
[image:22.599.320.522.75.101.2]セオ・ウエゥセョョ。ゥイ・@ distributed, and the number of people IOtervlewed can be seen in Table I below.
Table I. Summary of the fieldwork
587 3,909
107 26 52 119
107 26 52 119
69 26 40 108
64% 100% 77% 91%
5 3 2 3
10 8 28
33
aョ。ャケウセウN@ The data was analysed using mean comparISon and post hoc analysis to see the different among the cases. While the analysis within each case used correlation analysis. The qualitative data was used to enrich the finding and to give contextual sense to the quantitative analysis.
3. Results and Discussion
The discussion (If the results will begin by analysing the difference in the levels of information sharing and psychological empowerment; and is then followed by discussing the relationship between information sharing and psychological empowerment.
The levels of information sharing across the companies are significantly different. FoodCo has the highest information sharing index among the cases (see Table 2). Statistically FoodCo is the highest and significantly different from ChernCo aild WoodCo, while SteelCo is inbetween and indifferent from either FoodCo or ChernCo and WoodCo. FoodCo is clearly the highest since it employs various participation initiatives especially TQM. A great range of quality and productivity mformation is publicly given. The channels include quality circles, quality ceremony, and related activities. SteelCo has a similar approach though not
セウ@ ・クエ・ョセゥカ・@ as FoodCo, but problems in Implementmg TQM inhibit the amount and the quality of information which may flow. The informal approach of the supervisors· also contributes to the limited information sharing since informal communication tends to involve limited numbers of individuals. On the other hand, thl;: strict control at ChernCo and WoodCo may explain the difference. While WoodCo uses close supervision to control employees, ChernCo adopts formal SOP controls. These types of control limit the flow of information in the companies since this is usually under tight control. The statemel"!t of the human resource manager at.ChemCo, that information is deliberately
セッョエイッャャ・、@ In order to make employees undisturbed,
IS an obvious example that information flow is
strictly controlled in the company. Table 2. Comparison of empowerment and
information index across the cOlmoames
• Meaning 5.75 5.71 5.51 5.46 560
• Competence 5.46 5.59 5.43 5.12 5.40
• Choice 4.15 4.28 4.03 3.73 4.05
• Impact 4.85 4.83 4.28 4.43 4.60
*
*
Internet and Information Technology in Modern Organizations: Challenges & Answers 350
lnfonnation
Avg=Average
** the mean difference is significant at the .0 I level (2tailed).
*
the mean difference is significant at the .05 level (2tailed).Even though there are differences in the information sharing index, we need to be alert to the use of the index. First, there is a common opinion across the cases that the type of information shared in the companies is generally generated for the management interest. The range of information listed, which is regarded as important information for empowerment, clearly serves the company's concern, not the workers'.
•
The workers in almost every company studied complained that the information is given to make them work harder. The most common information received related to company problems (deviation of expected performance) and required the workers to improve the quality of their work. It seems that information was used selectively to enable managers to reriuce negative divergences and exploit the positive divergences which individuals make. As Braverman (1974) says the prioritisation of information in the manager's role is the key to scientific management. Similarly Webster and Robins (1993) argile that information can be used to continue and extend the established control mechanisms. In similar vein, Marchington and Grugulis (200 I) argue that information sharing is no more than a cascade' of infor11}ation from management to employees, which ignores the employee contribution. This one way information flow rather than being seen as empowering could more easily be interpreted instead as indoctrinating, emasculating, and controlling.Second, the information index ignores the depth, usefulness, and quality of information given. Instead of the extensiveness, other important dimensions are not considered. For example, the type of corporate performance shared with employees could have different effects. The company could explain its performance to employces, yet hide some vital information in order to control employees' reactions; or use performance information such as decreasing profit or market share to make employees work harder. Third, the information listed is based on an assumption that the practice is the best practice of information sharing for every organisation. For example, information about performance and competitor were used as the best proxy of information without considering the variety and the problematic implementation of such information in organisation.
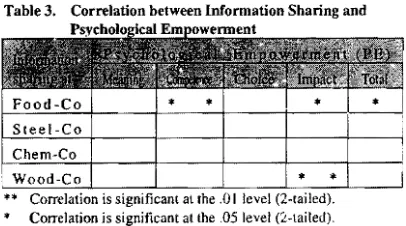
In terms of psychological empowerment, all the cases show high levels of it. This can be seen in the empowerment scores which are in the neighbourhood of five (see Table 3). FoodCo and SteelCo show higher scores than WoodCo and ChemCo. Statistically, there is a significant
difference in overall psychological empowerment levels between the four companies. The post hoc test shows that WoodCo's psychological empowerment level is significantly different from SteelCo and FoodCo, while there is no significant different between ChemCo, SteelCo, and FoodCo. Thus, the difference is mainly because WoodCo has the lowest scale.
Before discussing the relationships between information and psychological empowerment, there is an important finding that needs more attention. In each company, choice and impact are almost lower than meaning and competence dimensions. Choice and impact indices in each company are around four (the choice index is 4.05 and the impact index is 4.60), while meaning and competence indices are always above five (the meaning index is 5.60 and the competence index is 5.40). This fmding is similar to Spreitzer's (1995) surveys on different employee groups: midlevel managers, clerical workers, and frontline employees; Siegal and Gardner's (1999) study on employees in a manufacturing company; and Kraimer et al.' s (1999) survey on nursing professionals. This similar pattern to the dimensions of psychological empowerment creates some interesting questions for further exploration. First, though many studies support the existence of the four dimensions of empowerment, the choice and impact dimensions could be the most important measures when viewed from a structural perspective. Though the approach is psychological, this notion of psychological empowerment is originally conceptualised from the root of power and' control construct of Conger and Kanungo (1988). Feelings of choice which reflect autonomy or having control over ones' work and feelings of impact which indicate significant influences over strategic, administrative, or operational outcomes are closer to structural perspectives of empowerment. Choice can be regarded as power potential while impact reflects actual power (Kraimcr et ai 1999). This note is important when we analyse the relationship between structural and psychological empowerment in the next section. Second, some studies also report that meaning and competence are distmct dimensions but choice/selfdetermination and impact can come together as one dimension (Full ford and Enz, 1995). Therefore, Wall, Wood, and Leach (2004) suggest further qualification for the measures as Spreitzer (1995) comments that the measures need continued refinements. Finally, there is a possibility that the dimensions are sequentially related. For example, choice can be a precursor of meaning while competence can be a precursor of impact.
Internet and Information Technology in Modern Organizations: Challenges & Answers 351
psychological empowerment but it does not in other circumstances.
[image:24.599.97.300.195.308.2]There are some possible explanations of this finding. First, at FoodCo, the relationships are significant since psychological empowerment at FoodCo is at high level. It can be argued that information influences the feeling of empowerment when this is at a high level. In other words, information is relevant when individual has reached a certain level of psychological empowerment.
Table 3. Correlation between Information Sharing and
** Correlation is significant at the .01 level (2tailed). Correlation is significant at the .05 level (:itailed).
Second, since the relationship between information and psychological empowerment is not consistent, contextual factors might influence the lir.ks. The factors can be psychologicai, individual, and organisational. Therefore, contextual factors beyond the relationship need to be explored further. Spreitzer (1995) mentions a persona!ity variable and individual difference factors such as self esteem and locus of control
Third, one of the possible organisational factors is the extensiveness of FoodCo in using various involvement techniques. FoodCo has the mosl extensive empowerment climate and the organisational environment is supportive for psychological empowerment. While in other cases, the control climate dominated the environment at ChernCo, WoodCo, and SteelCo. At WoodCo, control is manifested in close personal supervision, while at ChernCo it shows in standard operating procedures. Furthermore, closer analysis can be done by looking at which psychological dimensions are influenced by information. We find that at FoodCo competence and impact dimensions are significantly influenced by information. I argue that information about individual performance will influence the feeling of competence, while information about company or unit performance will influence the feeling of impact.
Fourth, the measures of both information and psychological empowerment might fail to reflect the complexity of information sharing and empowerment at the workplace. Information measure has considered the extensiveness of information issues and but not the degree of information shared, while psychological empowerment has only measure the cognitive intrapersonal element of individual, while ignoring
the interpersonal and behavioural elements (Zimmerman, 2000)
Fifth, the reality of information in organisation might contribute to the relationship given the facts that information sharing gives only limited information to employees. This study found employees were given information as a condition to make them work harder. Therefore, information is not genuinely intended to empower the workers. This finding supports some studies that doubt the impact of information (see Wagner, 1994).
Finally, I would argue that in certain circumstances the psychological empowerment construct is not relevant especially when the organisation has collective culture. Adapting the notion of co!lective-efficacy of Lam, Chen, and Schaubroek (2002) I suggest that the development of collective empowerment is more appropriate. As discussed before, Spreitzer'S psychological empowerment is borrowed from selfefficacy, therefore it can be regarded as selfempowerment. In the Indonesian case, where collective culture is evident, the conception of collectiveempowerment could be useful. For example, the relationship between information sharing and psychological empowerment at WoodCo and SteelCo where the individual culture IS more evident than at FoodCo may be
explained better if collective empowerment is used rather than selfempowerment.
4. Conclusions
The .levels of information sharing and psychological . empowerment were' found different across the companies studied, The differences might be explained by the different structural initiatives like TQM employed by each organisation.
The relationship between information sharing and empowerment is not consistent in each case. Therefore, the universal effect of information sharing on empowerment is not confirmed. The contextual factors in which information influencing psychological empowerment need further analysis. The more complete dimensions in measuring information sharing and psychological empowerment are argued able to give better understanding ofboth variables and their relationships.
5. References
[1] Bowen, D.E. and Lawler III, E.E (1992). Empowerment of Service Workers: What, Why, How, and When. Sloan Management Review, 33(3), 3139.
[2J Bowen, D.E. and Lawler III, E.E (1995). Empowering Service Employees. Sloan Management Review, Summer, 7384.
Internet and Information Technology in Modern Organizations: Challenges & Answers 352
[4] Conger, J. A, and Kanungo, R. N. (1988). The empowerment process: integrating
[5] Fulford M.D. and Enz, C.A. (1995). The impact of empowerment on service employees. Journal of Manageri al Issues, 7: 161175.
[6] Fuller, 1. B., Morrison, R., Jones, L., Bridger, D. & Brown, V. (1999). The Effect of Empowerment on Transformational Leadership and Job Satisfaction. Journal of Social Psycholmty,
139(3),
[7] Hermawan, A (1997) Terpedaya dengan Pemberdayaan (Disempowered by Empowermem). Agrimedia 3 (1), 1997.
[8] Kanter, R. M. (1977). Men and women of the corporation. New York: Basic Books.
[9] Koberg, C. S., Boss, R. W., Senjem, J. C. &
Goodman, E. A. (1999). Antecedents and outcomes of empowerment. Group & Organisation Management, 24( 1),
[10] Kraimer, M.L., Seibert, S.E. & Liden, R.C. (1999). Psychological Empowerment as a multidimentional construct: a test of construct validity. Educational & Psychological Measurement, 59( 1),
[11] Kroeker, C.J. (1995). Individual, organisational, and societal empowerment a study of processes in a Nicaraguan agricultural cooperatives. American Journal of Community Psychology; 23(5),749 764.
[12]Lam, S.S.K., Chen,' X" and Schaubroek, J. (2002) Participati ve. decision making and employee performance in different cultures: the moderating effects of allocentrismlidiocentrism and efficacacy. Academy of Management Journal 45(5):905914.
[l3] Lashley, C. (1999). Employee empowerment in services: a framework for analysis. Personnel Review, 28(3), 169191.
[14J Lashley, C. (2000). Empowerment through involvement: a case study of TGI Fridays restaurants. Personnel Review, 29(6), 791815. [15] Lashley, C. and McGoldrick, J. (1994). The Limit of Empowerment: A Critical Assesment of Human Resource Strategy for Hospitality Operations. Empowerment in Organisation!h..2(3), 2538.
[16] Lawler, E. E., Mohrman, S.A, and Ledford, G.E., Jr. (1995). Creating High Performance Organizations. San Francisco: JosseyBass. [ 17] Marchington, M. and Grugulis, I. (2000). 'Best Practice' Human Resource management: Perfect Opportunity or dangerous Illusion? International Journal of Human Resource Management. 11(6), 11041124.
[18] Marchington, M. and Wilkinson, A. (2005), Human Resource Management at Work, CIPD, London.
[19] Sewell, G., and Wilkinson, B. (1992) "Someone to Watch Over Me: Surveillance, Discipline and the JustinTime Labor Process," Sociology 26(2): 271-289.
[20] Siegall, M. and Gardner, S. (2000) Contextual factors of psychological cmpowerment. Pcrsonnel
rセカゥ・キ@ 29(5-6): 703-722.
[21] Spreitzer, G. M. (! 995). Psychological empowerment in the workplace: Dimensions,
measurement, and validation. Academy of
Management Journal, 38(5), 1442-1465.
[22] Spreitzer, G. M. (1996). Social structural characteristics of psychological empowennent. Academy of Management Journal, 39(2), 483-504.
[23] Spreitzer, G. M., Janasz, S.C.D. & Quinn. R.E (1999). Empowered to lead: the role of psychological
empowerment in leadership. Journal of
Organisational Behaviour, 20, 511 セURVN@
[24] Spreitzer, G. M., Kizilos, M. A & Nason, S. W. (1997). A dimensional analysis of the relationship
betwecn psychological empowerment and
effectiveness, satisfaction, and strain. Journal of Management, 23, 679-704.
[25] Thomas, K. W., and Velthouse, B. A. (1990). Cognitive elements of empowerment. AcademLQf Management Review, 15(4),666-681.
[26] Wagner, J.A (1994) Participations effects on performance a.nd satisfaction: A reconsideration of research evidence. Academy of Management Review 19: 312-330.
[27] Wall, T.B., Wood, S.J., and Leach, DJ. (2004