This internship entitled "Internship on Routing and Switching" submitted by Sourav Sarkar ID No to the Department of Computer Science and Engineering, Daffodil International University has been accepted as satisfactory in partial fulfillment of the requirements for the degree of B.Sc. Department of Computer Science and Engineering Faculty of Natural Sciences and Information Technology Påskelilje International University. Gazi Zahirul Islam, Assistant Professor, Department of Computer Science and Engineering, Daffodil International University, in partial fulfillment of the requirements for the degree of Bachelor of Science in Computer Science and Engineering.
Gazi Zahirul Islam, Assistant Professor, Department of Computer Science and Engineering, Daffodil International University, Dhaka for his wholehearted supervision. His input during the development of the ideas in this report contributed substantially to the completion of this work. CSL Training is one of the largest ICT Training Center (Cisco, Linux, Microsoft, MikroTik, Security, Oracle, Juniper, VMware, Zimbra, Azure, Asterisk, Huawei) in Bangladesh.
As part of my BSc in Computer Science I completed my internship on routing and switching. As students of computer science engineering, we have acquired a lot of theoretical knowledge, but we are not skilled in practical matters. Currently, the popularity of routing and switching is increasing day by day all over the world.
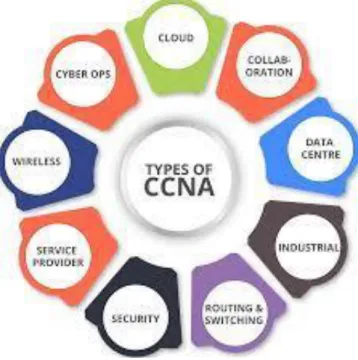
Cisco typically offers four levels of routing and switching certification, each with an increasing level of efficiency.
Internship Objectives
Introduction to the Company
Report Layout
ORGANIZATION
- Introduction
- Product and Market Situation
- Target Group
- SWOT Analysis Strength
The financial problem is to improve the area of their training and the area of the organization, which will greatly reduce the financial problem.
INTRODUCTION TO CCNA
Introduction to CCNA
INTRODUCTION TO OSI AND TCP/IP REFERENCE MODEL
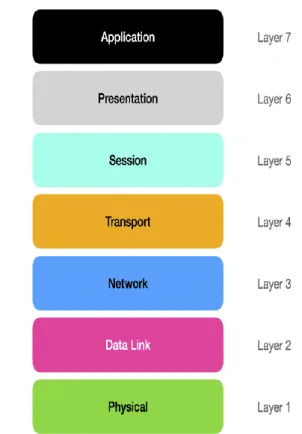
Introduction to OSI reference model
Application layer: The highest level of the OSI model is the application layer that interacts with an application program. Presentation Layer: The job of the presentation layer is to take data from the application layer and convert the subsequent layers into an understandable format. Session Layer: The session layer acts as a connector between the source and destination devices and maintains that connection until it is lost.
This session requires a logical connection to the layer that should be established based on the needs of the end user. Transport Layer: The transport layer ensures that data from the session layer is reliably delivered to another guest using different networks and further maintains the quality of downstream service functions. The transport layer recognizes the data transfer and sends the next data if no error occurred.
TCP usually confirms the sending of data via communication to the receiver when the message is passed, but UDP sends the data without any communication. This means that the TCP protocol always ensures the sending of data, while the UTP protocol does not ensure the sending of money, so it often reaches the data destination. Network Layer: The primary function of the network layer is to transfer data from one location to another and through other networks.
This means that the network layer selects the appropriate network route and forwards it to the transport layer for the packed data stack. Data Link Layer: The physical layer transmits data from one device to another in an error-free manner and transmits data in frame form. The three main steps at the data link level are to handle errors in the transmission, to control the data flow, and to provide a specific interface to the network level.
Physical Layer: The function of the physical layer is to define the electrical and physical property of the data link. This layer is used to transport data from one place to another through various connectors. It has nothing to do with physical level protocols or other high level items. This layer transfers data from one device to another in a networked computer bit.
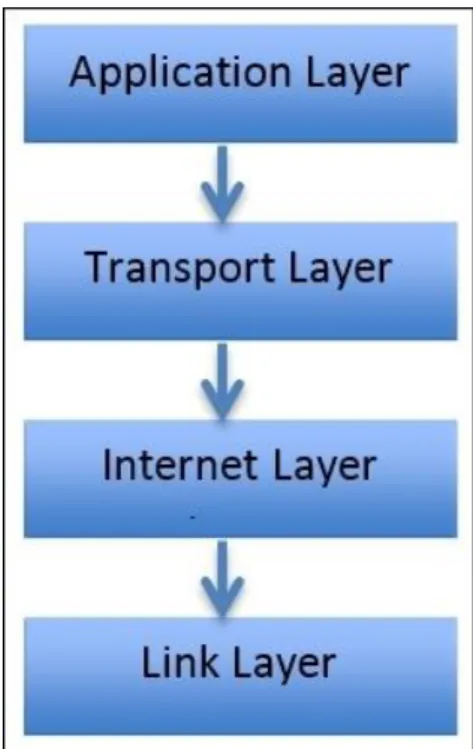
Introduction to TCP/IP reference model
ABOUT PHYSICAL AND LOGICAL ADDRESS
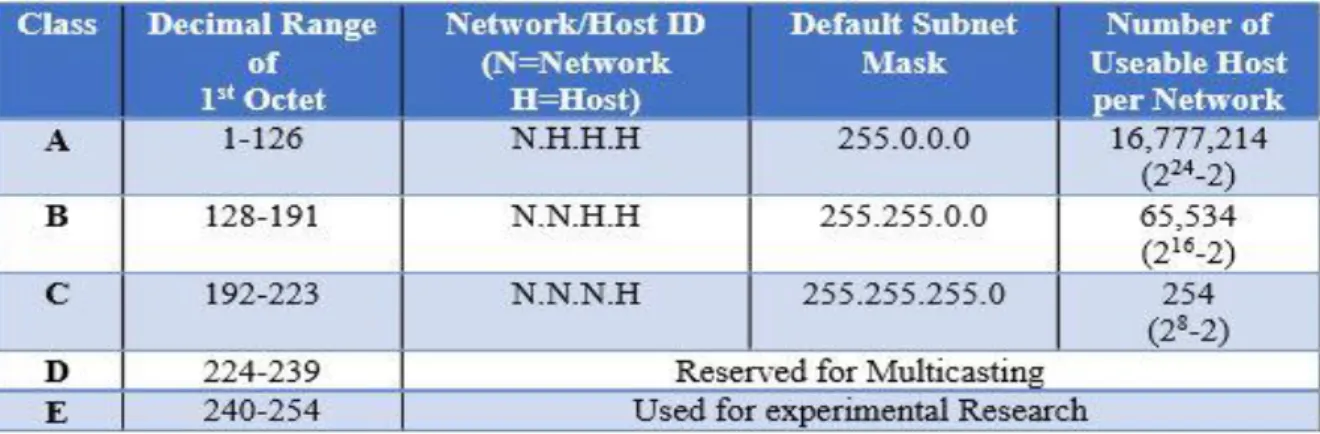
- About IP Address
- Classes of IP
- Private and Public IP Private IP
- IP Subnetting
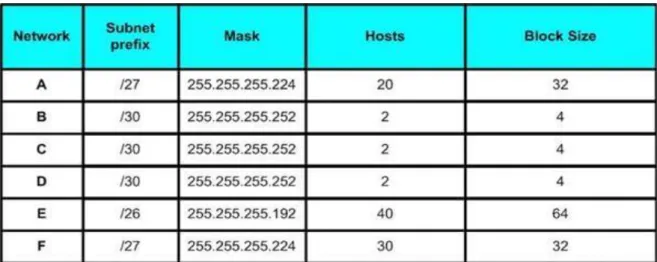
- Variable Length Subnet Mask (VLSM)
- Working with VLSM Network
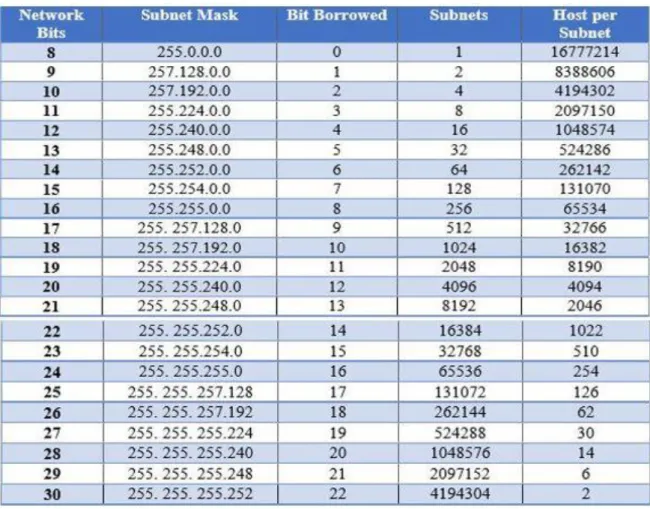
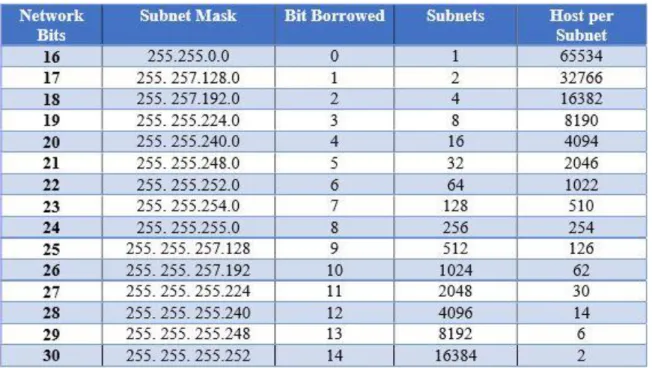
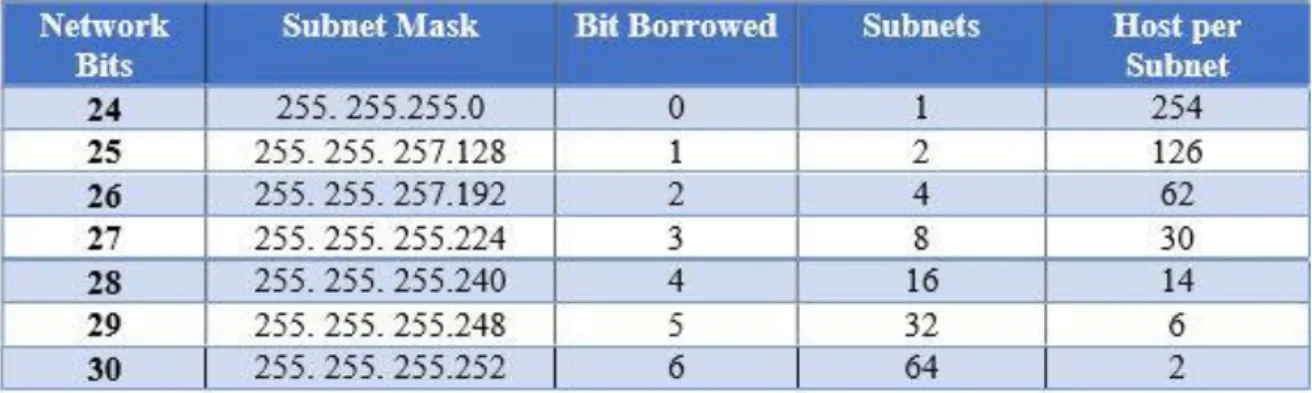
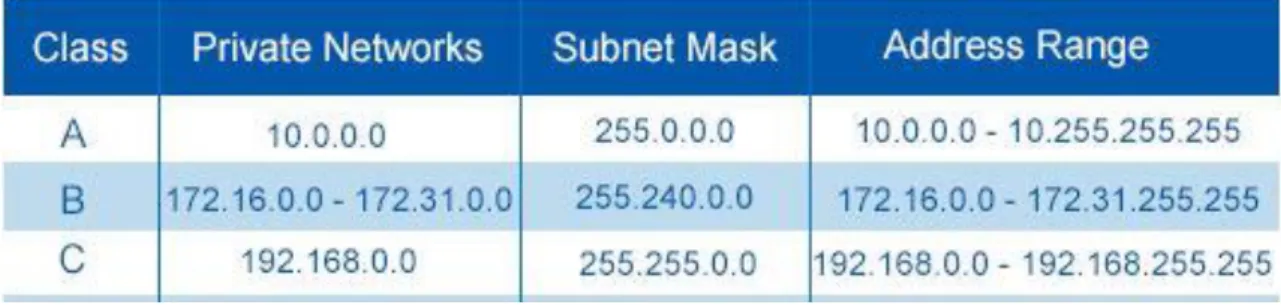
Private IP is an IP address that is kept for internal use in addition to public IP. If your tenant accesses a resource directly from the Internet, it must have a public IP address. Sub-Netting allows the creation of countless logical networks that refer to a single Class A, B or C network.
If we don't use subnetting, we will only be able to use one network instead of one network from different classes like A, B or C, which is not possible at all. Each device that connects to the work performed by the network/subnet has its own IP address. To create a subnet from the host ID part of the address, you need to extend the natural mask by a few bits.
Subnetting is done by choosing an appropriate mask to designate the number of hosts on the network, called a subnet mask. A subnet's network address can be a valid IP address from the subnet that devices can no longer use. Variable-Length Subnet Masking (VLSM) "subnetting" means that VLSM allows network engineers to divide an IP address into subnets of different sizes, allowing different host IPs to be distributed correctly without losing IP.
NETWORKING TOOLS
- Router
- Switch
- Fiber Optic Cable
- Twisted Pair Cable
All network devices connected to a switch are identified by their network address, the switch improves network security and efficiency. An Ethernet switch to create a separate domain for each switch port and the data link layer (layer 2) of the Open System Interconnection Model is required. Each device is connected to a switching port and can transfer data to another port and transmissions will not be interrupted.
Smart switches provide some management and segmentation, quality of service and protection, so they can be an affordable alternative to modular switches. Among fixed-configuration switches, the switches are designed to provide the most comprehensive feature set for optimal user experience, security arrangements, fine-grained control and network performance, and scalability. Fiber optic cable is a network of wires containing strands of glass fiber in a sheath.
Better than wired cable because fiber optic cables provide high bandwidth and transmit data over long distances without any problems. Each light particle (photon) continuously bounces through the bottom of the tube with an internal mirror-like reflection. Usually used for signal transmission in HD televisions because they have higher bandwidth and can operate faster.
NTT Japan has demonstrated with a single fiber cable capable of transmitting 1 petabit (1015 bits / second) per second over a distance of up to 50 kilometers. Twisted pair cable is one of the tools that commonly provides direction to broadcast media. A twisted pair cable consists of two different types of insulated copper wire that are twisted together and run in parallel.
One of the two wires is used to transmit data and the other wire is used for ground reference. There are usually two types of twisted pair cables: one is unshielded twisted pair (UTP) and the other is shielded twisted pair (STP). Shielded twisted pair cable consists of a metal foil with the coils binding each pair of insulated conductors.

ROUTER CONFIGURATION
- Platform
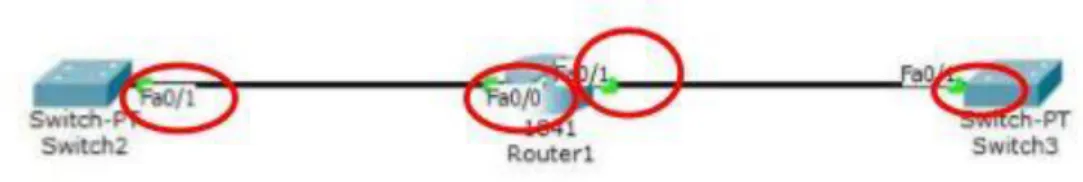
- Router Interfaces Configuration
- Static Routing
- Dynamic Routing
- Routing Information Protocol (RIP)
- RIP Configuration
- Enhanced Interior Gateway Routing Protocol (EIGRP)
- EIGRP Configuration
- Open Shortest Path First (OSPF)
Using router commands, administrators can enter relevant information about the desired interface. Or it may be important that another administrator later tries to resolve the problem or reconfigure the interface. For a full connection, a full static route must be configured on each router on each network.
Static router routes are typically configured by the router to route from a specific network to a stub network. Static routing generates very little load on all other router CPUs and generates no traffic when routing on all other routers. This routing can have complete control over the routing behavior of the network and then leave it to the network administrator.
Dynamic routing is a strategy to learn about routing information and choose the main route in its routing table. A Dynamic Routing Protocol A router in networking chooses the best route in that routing table, and routers can determine another route if the original route is lost at any time. Routing Information Protocol (RIP) refers to a part of the IP Routing Protocol, an interior gateway protocol (IGP) that exchanges this routing information between an autonomous system (AS) and the route is designed accordingly.
Routers around a vector routing protocol exchange information by building relationships with neighbors around them. A new version of the obsolete Interior Gateway Routing Protocol (IGRP) is the Enhanced Interior Gateway Routing Protocol (EIGRP). A router stores all routing information in a neighborhood when EIGRP is running and searches for alternate routes when necessary.
If the router cannot find a suitable route, EIGRP helps its neighbors find an alternative route. This protocol is routed based on an algorithm and calculates the shortest path to reach the destination. To configure an OSPF router, it is important to configure an area assignment to enable the interface.
SWITCHING AND VLANS
Configuring Switch with VLAN’s
VLAN Trunk Protocol (VTP)
VTP Configuration
COMPETENCIES AND SMART PLAN
Competencies Earned
Smart Plan
Reflections
CONCLUSION AND FUTURE CAREER
Discussion and Conclusion
Scope for Further Career
APPENDICES