Updated BGP Active Dynamic Neighbor Triggered by ADVPN shortcut NEW on page 923 and Enabling Automatic Firmware Updates on page 2502. Updated Interface-Based Traffic Shaping with NP Acceleration on page 1435, Fortinet Security Fabric on page 2856, Components on page 2856 and Configuring the root FortiGate and downstream FortiGates on page 2861.
Differences between models
Low encryption models
Using the GUI
Connecting using a web browser
Menus
On select FortiGate models, this menu has additional functions that allow FortiSwitch units to be managed by the FortiGate. Security Fabric Access to the physical topology, logical topology, automation, and settings of the Fortinet Security Fabric.
Filters
Some tables allow you to edit content directly in that table or copy and paste rows. Right column header or click the gear icon to the left of the header row that appears when you hover over the headers.
Column settings
Click the dots or filter icon on the right side of the column header and select Resize to Content.
Editing objects
Copying rows
Entering values
Text strings
Numbers
GUI-based global search
Sort byRelevance displays the closest matching address objects at the top and the least matching at the bottom (0.0.0.0).
Loading artifacts from a CDN
Accessing additional support resources
Command palette
Recovering missing graphical components
Using the CLI
Connecting to the CLI
Console connection
Using the console cable, connect the console port of the FortiGate unit to the serial communications (COM) port on your management computer.
SSH access
Once the FortiGate is configured to accept SSH connections, use an SSH client on your management computer to connect to the CLI. This is normal if the management computer is connected directly to the FortiGate with no network hosts in between.
CLI basics
If three incorrect login or password attempts occur in a row, you will be logged out. If this happens, wait a minute, then reconnect and try to sign in again.
Help
Shortcuts and key commands
Command tree
Command abbreviation
Adding and removing options from lists
Environment variables
USERFROM The type of management access (ssh, jsconsole, and so on) and the IPv4 address of the administrator who configured the item.
Special characters
Using grep to filter command output
Language support and regular expressions
Screen paging
Changing the baud rate
Editing the configuration file
If you change the model number, the FortiGate will reject the configuration when you try to reset it. If correct, the configuration file is loaded and each line is checked for errors.
Command syntax
Notation
To modify lists that contain space-separated options, in most cases you must retype the entire list, including all the options you want to use and excluding any options you want to remove.
Optional values and ranges
Subcommands
Theeditsubcommand changes the command prompt to the name of the table value being edited, such as (27). This may result in being unable to connect to or log in to the FortiGate, requiring the FortiGate to be formatted and reset.
Field subcommands
Permissions
FortiExplorer for iOS requires iOS 10.0 or later and is compatible with iPhone, iPad and Apple TV. It is supported by FortiOS 5.6 and later, and is available on the App Store for iOS devices.
Getting started with FortiExplorer
You can connect wirelessly to FortiGate if your iOS device and FortiGate are both connected to the same wireless network. If the app has found the FortiGate device, the device's serial number will be displayed.
Running a security rating
Basic administration
Basic configuration
Configuring an interface
Configuring the hostname
Configuring the default route
Ensuring internet and FortiGuard connectivity
Using the default certificate for HTTPS administrative access
Registration
The CLI can be used to activate FortiGate Cloud without registration, or with a different FortiCloud account. A FortiCloud account that is not used for the support portal account cannot be used to register FortiGate.
Transfer a device to another FortiCloud account
Configuration backups
Backing up and restoring configurations from the GUI
When password masking is enabled, passwords and secrets will be replaced in the configuration file with FortinetPasswordMask. When prompted, select a location on the PC or USB drive to save the configuration file.
Backing up and restoring configurations from the CLI
This may be because the configuration file is for a different model or saved from a different version of the firmware. The password entered during the upload process does not match the one associated with the configuration file.
Configuration revision
Solution: Upload a configuration file that is for the correct FortiGate device model and firmware version. When revision control is enabled on your FortiGate unit and configuration backups have been made, a list of saved revisions of those backed up configurations is displayed.
Restore factory defaults
Configuration backup is done by default with firmware upgrades, but you can also configure it to be done every time you log off.
Secure file copy
Deregistering a FortiGate
If the FortiGate has been registered for less than three years, deregistration will fail.
Migrating a configuration with FortiConverter
When the conversion process is complete, you will receive an email and a notification in the FortiGate GUI. One-time upgrade prompt when a critical vulnerability is detected at login NEW When FortiOS detects a critical vulnerability, a one-time upgrade prompt is displayed after logging into FortiGate.
Diagnostics
LEDs
Blinking green Power detected, but the power supply is not supplying power or is in standby mode. Blinking yellow Power supply failure or warning events, or the power supply needs to be replaced.
Alarm levels
Troubleshooting your installation
- Check for equipment issues
- Check the physical network connections
- Verify that you can connect to the internal IP address of the FortiGate
- Check the FortiGate interface configurations
- Verify the security policy configuration
- Verify the static routing configuration
- Verify that you can connect to the Internet-facing interface’s IP address
- Verify that you can connect to the gateway provided by your ISP
- Verify that you can communicate from the FortiGate to the Internet
- Verify the DNS configurations of the FortiGate and the PCs
- Consider changing the MAC address of your external interface
- Check the FortiGate bridge table (transparent mode)
- Either reset the FortiGate to factory defaults or contact Fortinet Support for assistance
If you cannot connect to the interface, the FortiGate does not allow sessions from the internal interface to the Internet interface. If you cannot connect to the FortiGate GUI or CLI, you may be able to connect to FortiExplorer.
Using dashboards
You can customize the appearance of a standard dashboard to display data relevant to your Security Fabric, or you can combine widgets to create custom dashboards. Each dashboard contains a set of widgets that allow you to view detailed data and take action to prevent threats.
Using widgets
Best fit all columns Resize all the columns in a table to fit their contents. Group by this column Groups the table rows by the content in the selected column.
Widgets
Viewing device dashboards in the Security Fabric
Creating a fabric system and license dashboard
Dashboards
Resetting the default dashboard template
Status dashboard
Updating system information
Viewing Fabric devices
Viewing administrators
If the GUI is using the default HTTPS certificate, a warning appears where you can download the HTTPS CA certificate or change the HTTPS server certificate.
Viewing logs sent for remote logging source
Resource widgets
Security dashboard
Viewing session information for a compromised host
Network dashboard
Static & Dynamic Routing monitor
To view policy routes, click the screens drop-down menu at the top of the page and select Policy. To view neighbors and paths, click the on-screen drop-down menu and select the desired neighbor or path type.
DHCP monitor
To filter or configure a column in the table, hover over the column header and click the Filter/Configure Column button. In the toolbar, click Reservation > Create DHCP Reservation, or right-click the device and click Create DHCP Reservation.
IPsec monitor
SSL-VPN monitor
Assets & Identities
Assets
Assets and filtering
Adding MAC-based addresses to devices
Firewall Users monitor
WiFi dashboard
To learn more about using and editing dashboards and widgets, see Dashboard and Monitors on page 101. This section describes the following monitors available for the WiFi Dashboard:. l FortiAP status monitor on page 128. l Clients from FortiAP monitor on page 130.
Clients by FortiAP monitor
Monitors
Non-FortiView monitors
You can also add FortiView monitors directly to the tree menu using the Add (+) button.
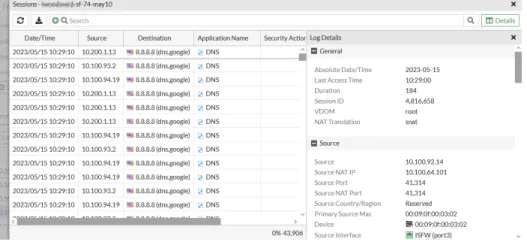
Core FortiView monitors
FortiView Policies Shows Top Policies by traffic volume and breakdown by Policy Number FortiView Sessions Shows Top Sessions by traffic source and can be used to terminate sessions. You can quarantine a host and ban an IP from all core FortiView monitors.
Adding FortiView monitors
Monitors by category
Cloud Applications Bytes/Sessions/Files (Up/Down) Displays the top cloud applications and summary by application. Countries/Regions Bytes/Sessions/Bandwidth/Packets Show top countries/regions and breakdown by country/region.
Using the FortiView interface
Real-time and historical charts
Data source
When Data Source is set to Best Available Device, FortiAnalyzer is selected if available, then FortiGate Cloud, then FortiGate.
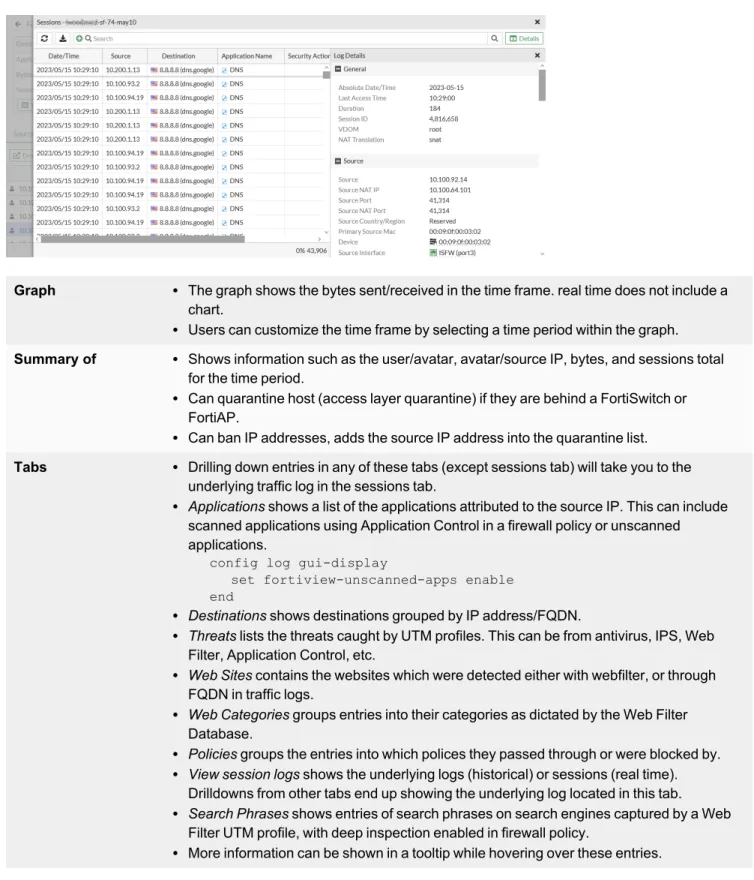
Drilldown information
Summary of l Shows information such as user/avatar, avatar/source IP, bytes and sessions total for the time period.
Enabling FortiView from devices
You can filter the sessions displayed in the sessions table by setting the available filtering options. You can use the supported filters in the CLI to display only the data you need.
Requirements
For example, you may want to view all sessions from a device with a particular IP address by adding the Source IP filter. Likewise, you may need to target all sessions with a particular DestinationIP and Destination Port, and so on.
Viewing top websites and sources by category
Viewing the web filter category
The category name also appears in the category column on the FortiView web page monitor and when opened in the FortiView resource monitor.
Cloud application view
Viewing cloud applications
Applications with cloud behavior
This example shows an application sensor without a lock icon, which means that this application sensor does not require SSL deep inspection.
Configuring the Cloud Applications monitor
This shows the number of local network users who logged into YouTube and played YouTube videos. This shows the number of local network users who logged into Dropbox and uploaded or downloaded files.
Using the Cloud Applications monitor
Sessions monitored by SSL deep inspection (in this example, Youtube_Video.Play) captured deep information such as Application User, Application Details, etc. To display a specific time period, select and drag on the timeline chart to display only the data for that time period.
Top application: YouTube example
Monitoring network traffic with SSL deep inspection
This application sensor does not rely on SSL deep inspection and thus does not have a cloud or lock icon. Also note that the Application Checker IDis38569 indicates that this item is activated by the application sensorYouTube_Video.Play.
Monitoring network traffic without SSL deep inspection
On the FortiGate, go to Log and Report > Security Events, select Application Control, and search for log entries for browsing and playing YouTube videos. On the FortiGate, go to Log and Report > Security Events and look for log entries for browsing and playing YouTube videos in the Application Control Card.
Interfaces
VLANs can be used on a FortiGate in NAT or transparent mode, and the FortiGate functions differently depending on the operating mode See VLAN on page 190 for more information. See OSPF with IPsec VPN for network redundancy on page 1943, GRE over IPsec on page 1860, and Cisco GRE-over-IPsec VPN on page 1890 for more information.
Interface settings
The values can be entered manually or saved via a speed test performed on the interface. IP/Netmask If Addressing Mode is set to Manual, enter an IPv4 address and subnet mask for the interface.
Configure administrative access to interfaces
For more details, see Performing hub-to-leg speed tests in per-dial IPsec tunnels on page 1060.
Because the speed is changed to 1000G, the media type setting automatically changes to sr4, and the forward error correction setting automatically changes to cl91-rs-fec.
Configure IPAM locally on the FortiGate
There is a conflict marker (warning icon) next to the IP address of FG019TM22004646 due to a conflict between the FG019TM22004646 root FortiGate's IPAM-assigned interface and the manually configured downstream FortiGate interface. If "Automatic conflict resolution" is disabled in IPAM settings, hover over the conflict marker and select Redistribute IP to manually reallocate the IP address.
Interface MTU packet size
To manually test the maximum MTU size on a route, you can use the ping command on a Windows computer. By reducing the TCP MSS, you can effectively reduce the packet MTU size.
One-arm sniffer
The one-arm sniffer can cause higher CPU usage and perform at a lower level than traditional inline scanning, which uses NTurbo or CP to accelerate traffic when present. The following example shows how to configure a file filter profile that blocks PDF and RAR files used in a one-arm snooping policy.
Interface migration wizard
The migration occurs automatically and the statuses for the object and reference change to Updated entry.
Captive portals
This page displays users who try to log in when user access is set to Allow Everyone. Rejected disclaimer page Appears if the user disagrees with the statement on the disclaimer page.
Physical interface
Most of the text and some of the HTML in the message can be changed. Disclaimer page A statement of legal responsibilities of the user and the host organization that the user must agree to before proceeding.
Displaying transceiver status information for SFP and SFP+ interfaces
This page is displayed to users trying to log in when user access is set to Restricted to groups. The Transceiver column is visible in the table showing the transceiver vendor name and part number.
VLAN
VLANs in NAT mode
In this case, both the FortiGate unit and the Cisco 2950 switch are installed and connected, and the basic configuration is complete.
VLANs in transparent mode
Next, we create security policies that allow packets to travel between the VLAN_100_int interface and the VLAN_100_ext interface. The same is required between the VLAN_200_int interface and the VLAN_200_ext interface, for a total of four security policies.
Virtual VLAN switch
In this example, two FortiGates in an HA cluster are connected to two ISP routers. See HA using a hardware switch to replace a physical switch on page 2633 for a similar example that does not use a VLAN switch.